The storage and safe administration of knowledge and passwords is without doubt one of the most necessary features within the crypto and blockchain world, and extra usually in all on-line environments.
Encryption, intense because the artwork of “hidden writings” able to changing plain textual content into encrypted textual content and vice versa, involves our support making it tough for hackers to permit unauthorized entry to sure networks and transactions.
Let’s delve into the totally different strategies by way of which encryption can shield beneficial data and safeguard passwords.
Symmetric and uneven password encryption within the crypto sector
Usually when speaking about password safety in cryptography, reference is made to 2 encryption strategies: symmetric and uneven.
That symmetric one refers to a sort of textual content encryption that makes use of a single key to encrypt and decrypt data:
The encryption key’s shared between sender and recipient and is often agreed upon prematurely: it represents the central ingredient that in cryptocurrencies permits customers to entry and handle their digital sources.
Symmetric encryption with a single key is without doubt one of the most typical means to guard passwords, transactions, and communication between working nodes.
When performing, for instance, a funds switch from one pockets to a different, it ensures that the data is learn and shared solely by two events concerned within the transaction, conserving the information protected from prying eyes.
Nevertheless, regardless of the benefits it brings, symmetric encryption has limitations when it comes to scalability and key administration.
Certainly, the necessity for communication in pairs drastically limits the growth of this observe in a system with many extra customers. On the identical time, extra customers suggest human errors within the administration and conservation of the so-called “non-public key”, which if misplaced results in the lack of crypto or knowledge saved within the digital pockets.
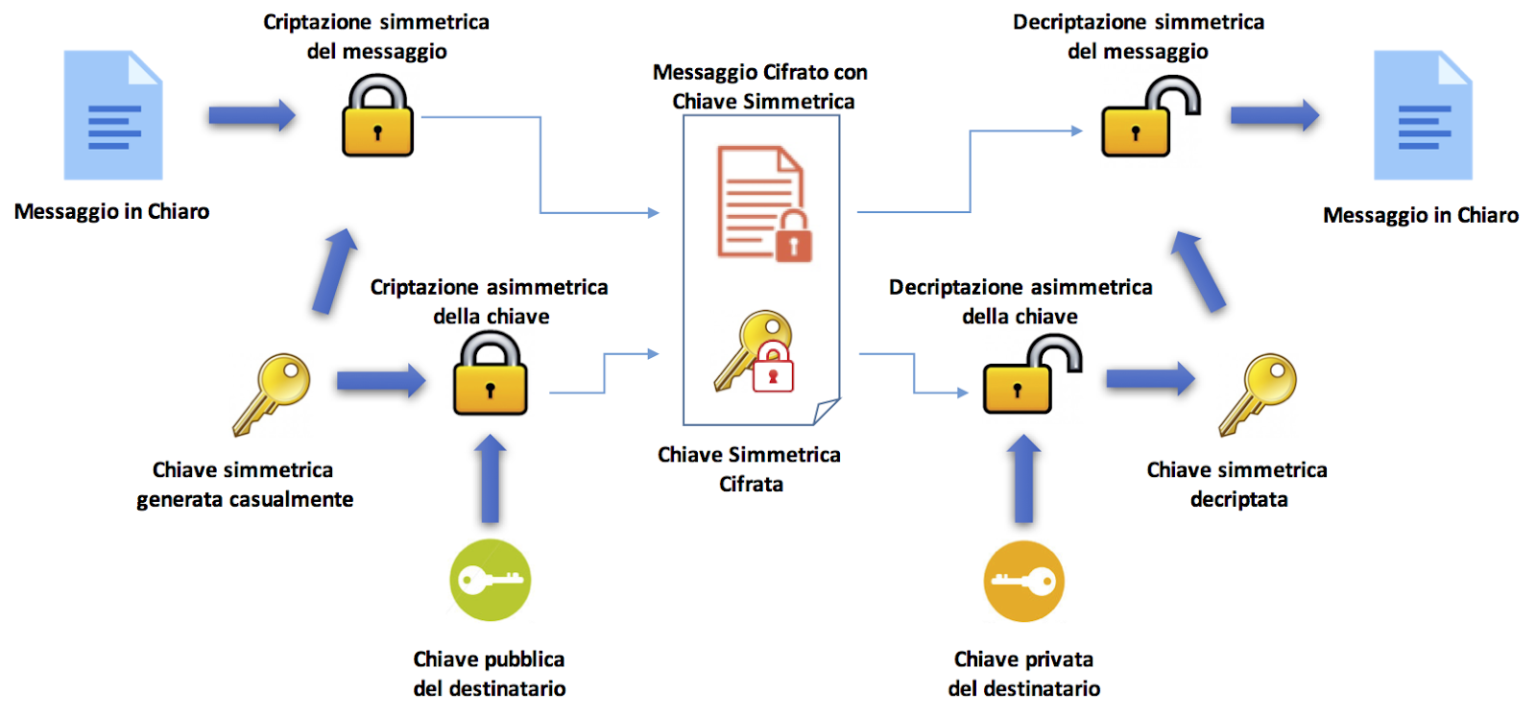
To beat these limitations, uneven cryptography involves our support by offering a pair of separate keys (private and non-private) within the encoding and decoding of passwords.
This extra degree of safety immediately will increase knowledge safety: the general public key will be shared with anybody on any community (like once we share our handle to obtain a cost in crypto), whereas the non-public key should be stored secret.
Each keys are generated by an algorithm that makes use of massive prime numbers to create two distinctive and mathematically linked keys.
Anyway, whoever possesses the general public key can encrypt a message, however solely the holder of the non-public counterpart can decrypt the textual content. We will think about this as if it have been an e-mail inbox: whoever holds the general public key can ship a message, however solely the proprietor of the non-public key can open the e-mail and skim the messages.
Non-custodial software program wallets like Belief Pockets or MetaMask use uneven cryptography to supply the best attainable safety to their customers.
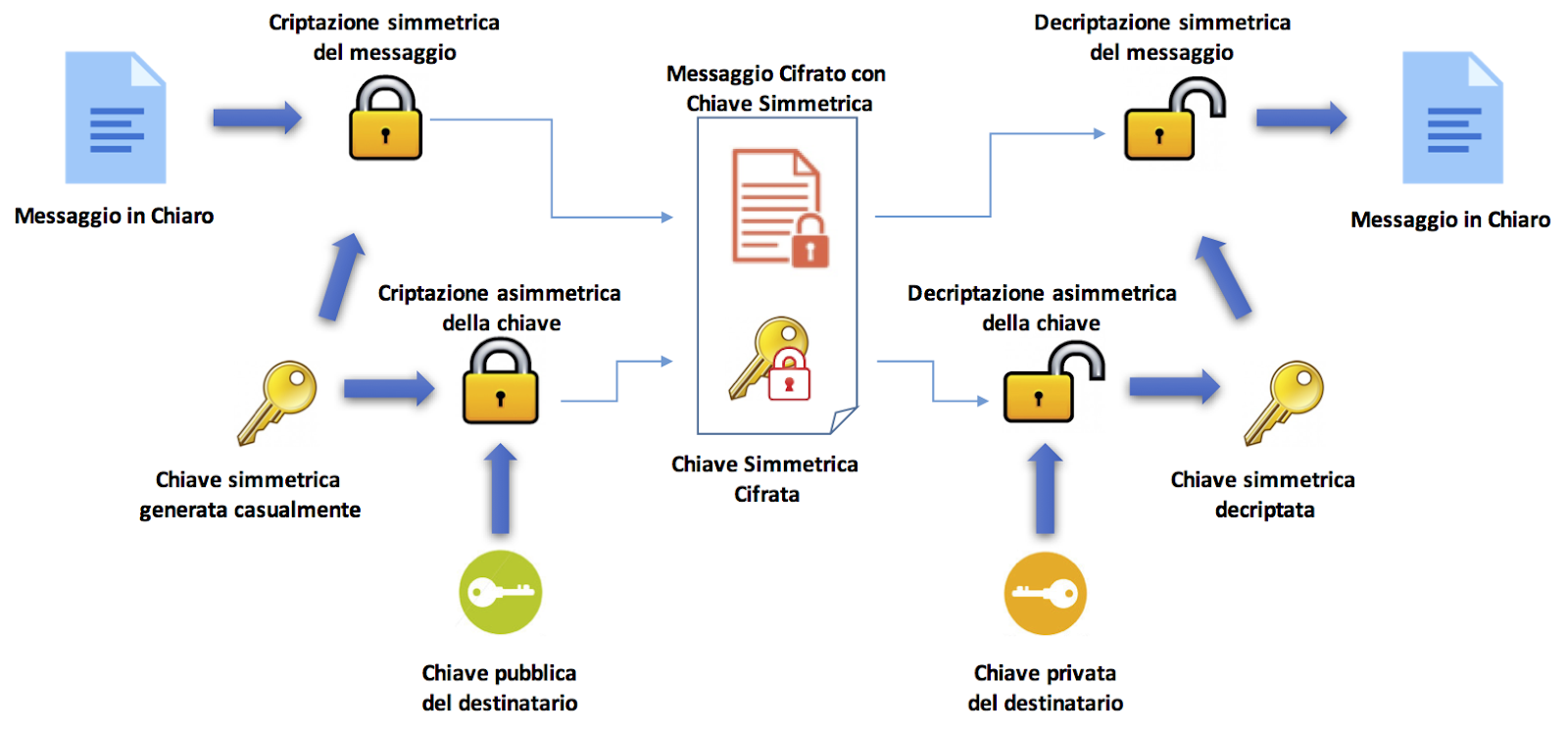
Supply: https://www.javaboss.it/crittografia-in-java/
The most typical codecs of encrypted passwords
Password encryption within the crypto and blockchain sector happens based on totally different codecs that can be utilized for various functions and provide totally different ranges of safety:
- MD5 (Message Digest 5):
The MD5 algorithm, developed by Ronald Rivest in 1991, generates a 128-bit hash (32 hexadecimal characters) from a variable-length enter.
It’s not thought-about safe as a result of vulnerabilities found in its algorithm. Nevertheless, it’s nonetheless utilized in some legacy contexts, for instance to confirm the integrity of information.
- SHA-1 (Safe Hash Algorithm 1):
SHA-1 generates a 160-bit hash (40 hexadecimal characters).
It’s not thought-about as safe because it as soon as was, having proven a number of vulnerabilities: it’s now usually changed by extra strong algorithms comparable to SHA-256 and SHA-3. Nevertheless, it’s nonetheless utilized in a variety of methods and new functions.
- Salt:
The salt is a random sequence of bits that’s added to the password earlier than calculating the hash.
It solves the issue of collisions (two totally different passwords producing the identical hash) in hashing strategies.
By including a salt, even an identical passwords may have utterly totally different hashes. This makes it tougher for attackers to decrypt passwords by way of brute power assaults.
- Bcrypt:
Bcrypt is a hashing algorithm particularly designed for password encryption.
Use a salt and a variety of iterations to decelerate the hash calculation. It’s broadly used to guard consumer passwords within the discipline of databases.
The selection of encryption format is dependent upon the particular wants of the reference system. These days, it’s advisable to make use of hashing algorithms comparable to bcrypt or SHA-2 to guard passwords and mitigate cyber assaults.
Hash capabilities and digital signatures
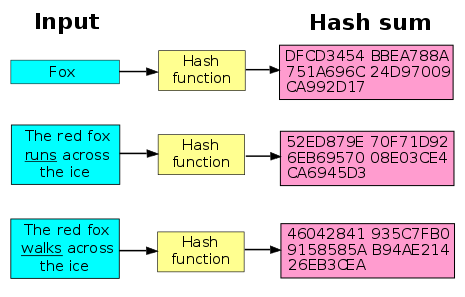
One other strategy to shield passwords and beneficial data in cryptocurrencies is to depend on hash capabilities, that’s algorithms that remodel any type of knowledge right into a string of characters of fastened size.
By utilizing strong hashing algorithms, we are able to successfully shield delicate data and stop cyber assaults.
Hash capabilities are irreversible: it isn’t attainable to transform a hash again into its unique knowledge. They’re important in knowledge administration on the blockchain as a result of they permit structuring data with out compromising its preliminary integrity
Hashes can even act as fingerprints for all encrypted passwords, defending the consumer in opposition to unauthorized actions on their account.
Certainly, any modification to the unique knowledge would lead to a brand new hash, which might not correspond to the unique supply and due to this fact wouldn’t be verifiable on the blockchain.
One other technique to make sure password safety, and extra particularly the authenticity and integrity of knowledge in a message, is to make use of the so-called “digital signatures” (uneven cryptography approach).
That is merely a way to make sure that the proprietor of these particular knowledge is approving the transaction. Usually, the sender creates the digital signature utilizing a non-public key to encrypt the signature knowledge, whereas the recipient obtains the signer’s public key to decrypt the information. This code represents irrefutable proof {that a} message has been created solely by the sender and has not been tampered with on-line.
When speaking about digital signatures, one instantly thinks of signature gadgets like Ledger, Trezor, and Bitbox that enable to validate a transaction earlier than it’s broadcasted to the remainder of a cryptographic community.
Nevertheless, watch out to not think about these gadgets as wallets: they don’t include your cryptocurrencies however solely mean you can approve the transactions essential to spend them.
We frequently say, “my crypto is ON my Ledger”.
However your digital belongings aren’t really saved bodily in your Ledger – they’re on the blockchain.
Your Ledger shops and protects your non-public keys and retains them protected so you may totally personal and handle your belongings.@iancr explains: pic.twitter.com/PGrmQIvKpV
— Ledger (@Ledger) Might 11, 2023